n8n – CVE-2025-68613: Critical RCE Vulnerability


In the world of cybersecurity, appearances can be deceiving. A file might look like an innocent image, but behind the scenes, it could also be a ZIP archive, a PDF, or even an executable. Such files are called polyglots — single files that are valid under multiple file formats at the same time.
Polyglots are fascinating from a technical standpoint, but they also pose serious security risks. Attackers often use them to bypass filters, sneak past antivirus solutions, or trick unsuspecting users into executing malicious code.
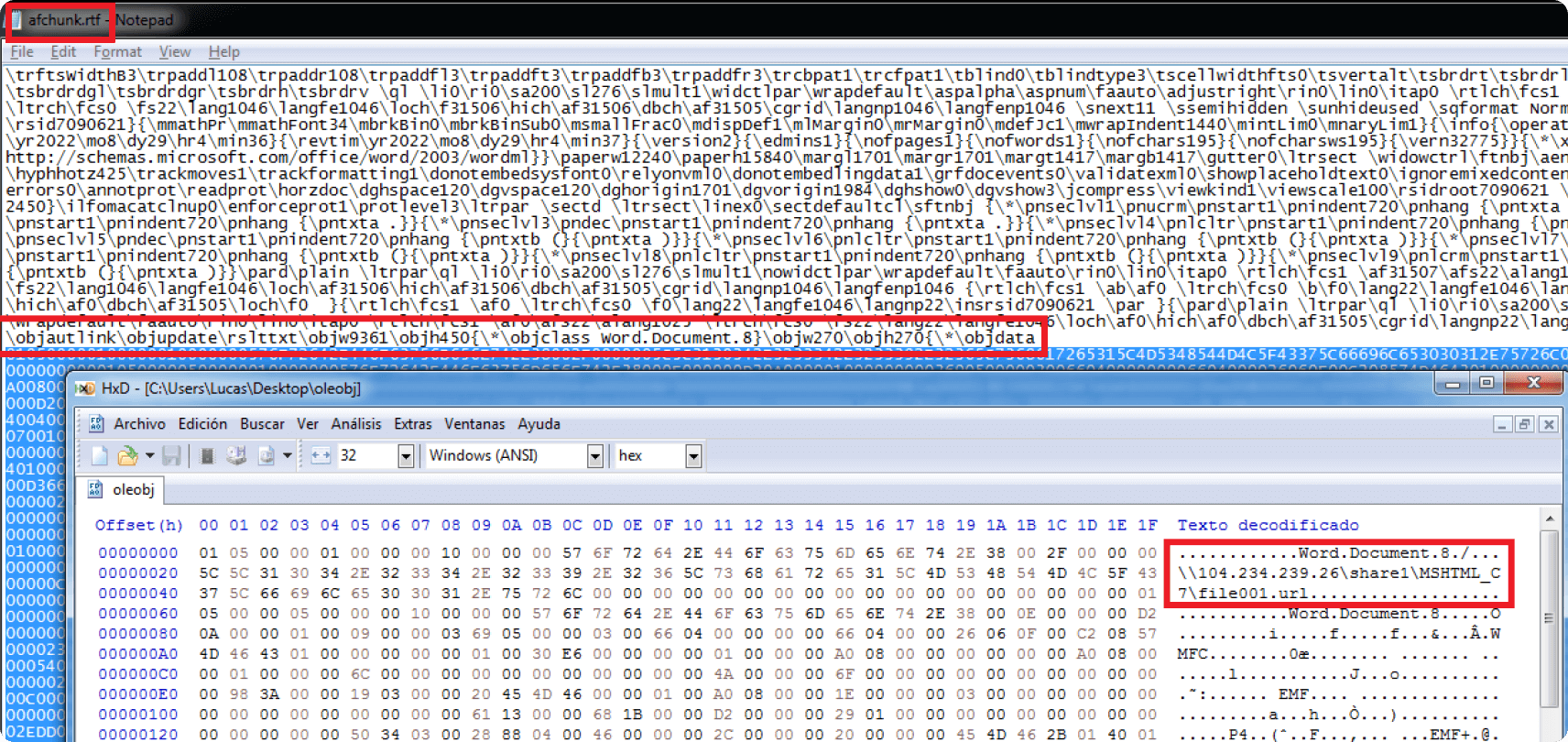
A polyglot file is crafted in such a way that it conforms to the specifications of two (or more) different file types simultaneously.
This dual nature makes polyglots powerful tools for both legitimate research and malicious exploitation.
To understand polyglots, you need to know about file signatures (magic numbers).
FF D8 FF50 4B 03 04%PDFBy carefully aligning headers and footers of two formats, attackers can create a file that satisfies both.
For example:
Polyglots have been used in multiple contexts:
One famous example is the GIFAR polyglot, which is both a GIF image and a Java Archive (JAR) file. Attackers used it to upload malicious Java code disguised as images on web servers.
⚠️ For educational purposes only — don’t use this maliciously.
Let’s create a JPG+ZIP polyglot:
test.jpg image and a secret.zip archive.cat ayanokouji1.png polyglot_file.zip > ayanokouji1.jpgNow:
open ayanokouji1.jpgunzip ayanokouji1.jpg
This works because image viewers only care about the start of the file,
while unzip looks for the ZIP footer.
Polyglots are not just fun hacks — they highlight deeper issues:
Understanding polyglots helps defenders improve detection and researchers design better security tools.
Here are some ways to mitigate risks:
binwalk, xxd, or file to inspect files.Polyglot files are like the chameleons of the digital world — blending into multiple environments at once. They showcase the creativity of hackers and researchers alike, but also warn us of the need for stronger file validation and security practices.
So, the next time you open a file that seems ordinary, remember: it might just be speaking more than one language.
Comments
Post a Comment